ExamNotes for Network+ N10-007 1.7 Summarize cloud concepts and their purpose
Click here to go back to the Network+ ExamNotes Table of Content
Cloud computing has become a part of every user’s daily interactions. Even your Smartwatch can store data in the cloud. Here we’ll look at the available cloud services, delivery models, connectivity, and the security aspects.
Click here if you want to view a video walkthrough of a Performance Based Question
Types of services
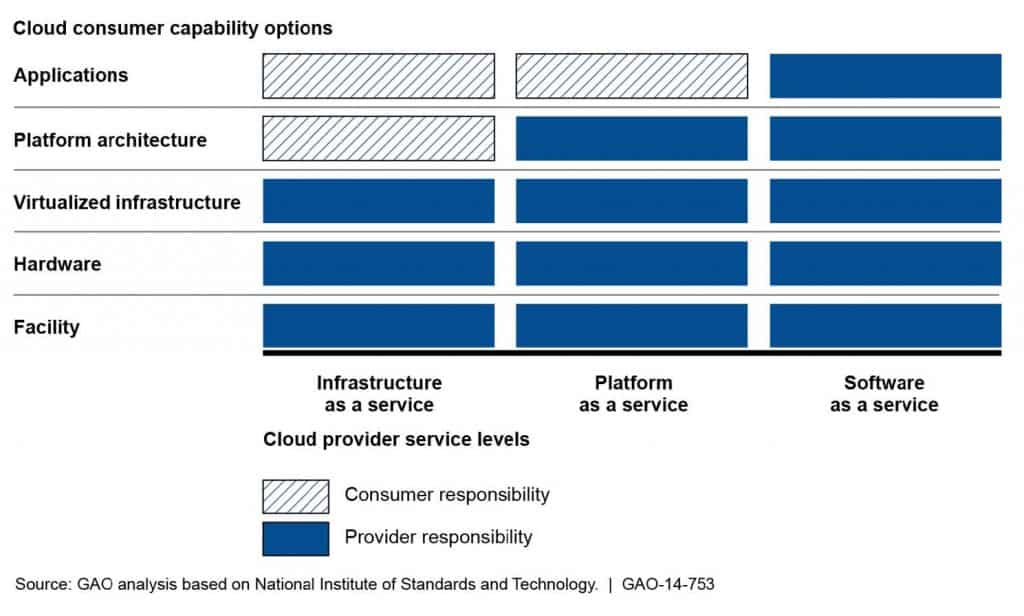
Cloud service levels are defined by the amount of responsibility assigned to a given service level as compared to a traditional network using virtualization. As a reference, a traditional network bears 100% of the responsibility for the workspace, hardware, virtual infrastructure, OS platform, and application software. The cloud vendor can provide varying levels of service based on the customer’s needs.
The types of cloud services are described below.
IaaS (Infrastructure as a Service) places the responsibility of application installation and management as well as backups and data management on the customer. Depending on the agreement, the customer may opt for hosted virtual desktops (HVD) from the vendor running on their hardware platform.
PaaS (Platform as a Service) places the responsibility of application installation, backups, and data management on the customer. The vendor provides the hardware, operating system, and related support software. Amazon Web Services, Google Cloud Platform, and Microsoft Azure are examples of this service level. This level is beneficial to developers who can test their work virtually.
SaaS (Software as a Service) is the most accessible and complete solution since it requires only an Internet browser interface. Applications, data management, and storage are provided by the vendor. Google and Microsoft both offer SaaS virtualized apps, such as Google Docs and Microsoft Office 365. This solution allows access to applications and services without any installation. Users can work from anywhere and on any device with a browser.
Here is a good illustration depicting the relationships across different service types.
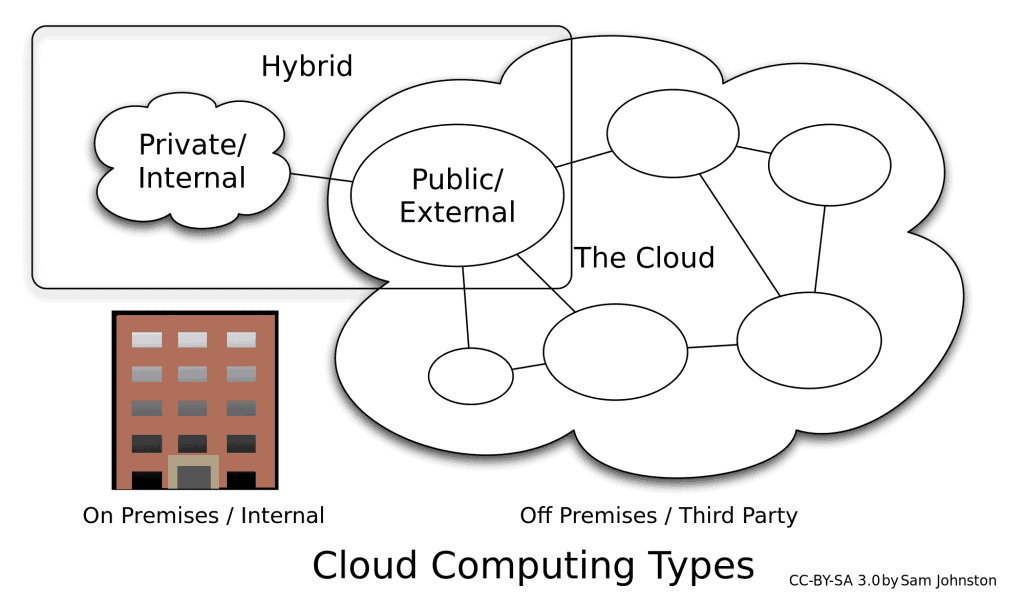
Cloud delivery mode
Cloud access is modeled as follows.
Public – A public cloud service is available to any party. The Internet is the best example of this service model and is also the least secure.
Private – A private cloud is hosted by an organization for its own internal use or for its users through remote access over WAN links. When hosted virtually, the scalability and accessibility of the virtual environment offers value. Internal hosting allows the organization to use existing resources which could be considerable.
Hybrid – A hybrid cloud uses whichever mix of cloud delivery modes is necessary to create a single model. An example of this is an organization that uses the private cloud for data management and storage while using a public cloud for messaging and email. This model can also be used as a transitional solution during the implementation of a total cloud solution.
Connectivity methods
Your connection to the cloud can be classified in the following ways.
Internet – This is a highly insecure option. While it is comparatively inexpensive and simple to use, there are erratic latency issues that could affect performance.
Remote access – These connections offer increased security by creating secure tunnels but are still subject to the quality issues of the Internet.
Leased line – This option reserves a predetermined bandwidth allocation between the customer and the cloud service provider, usually over a private WAN.
Dedicated connection – This is the most expensive connection method. Here, it is possible to connect from the customer location directly to the cloud provider. Since the majority of cloud providers have strategically located points of presence (PoP), access qualities are assured.
Security implications/considerations
Cloud security has several implications that could expose otherwise private data. Consider the cloud provider’s security and the security of the backups. Your stored data could be accessed by unauthorized parties or even authorized parties who disregard the confidentiality of the data. As a result, your cloud must adhere to the Government regulations regarding security, for example, HIPAA and financial security. Also, consider what happens to your data if your agreement lapses.
In order to protect your data, please consider performing the following:
A) Always get the most securely structured SLA from the cloud provider
B) Ensure that your link to the provider is equally secure.
C) Last but not least, use strong encryption.
The relationship between local and cloud resources
A customer’s local network will be secure (presumably) and offer the speed benefits of their network without the possibility of third-party access. Backups are fast and easy to restore. The expenses involved in running a local network are the infrastructure and IT staff, which may or may not be sufficient when it comes time to scale. Disaster recovery on the local network requires the support of additional locations, which could lead to a considerable cost.
Cloud storage offers greater scalability, user accessibility, and elasticity features when compared to local resources, making cloud storage a good solution. However, cloud storage does have concerns with regards to connectivity, speed, and above all security. Your cloud data is inaccessible if the internet connection is down anywhere between your location and the cloud. Backups can be uploaded ever 15 minutes to keep the data current. However, in the event of a failure, the restore time is considerable and resource intensive.
That’s it for objective 1.7 – Good luck on the test!
Click here to go back to the Network+ ExamNotes Table of Content