Welcome to ExamNotes by CertBlaster! This section will address objective 3.5 Given a scenario, troubleshoot common mobile OS and application security issues with appropriate tools. We will look at the common symptoms and the tools you will use to mitigate them.
Click here for the A+ Practice Test Bundle for A+ Exams 220-1001 & 220-1002
Signal drop/weak signal
Smartphone users are used to having signals drop as they travel. “Can you hear me now?” If you find yourself in an environment where you usually have a good signal and no longer connect reliably or the signal is weaker than usual you may have malware on the device. Whether it is cellular or Wi-Fi signal degradation malware is a primary consideration when diagnosing sub-par wireless communications. Obtain a malware scanner from a trusted source to check for malware.
Power drain
When your smartphone or tablet suddenly loses half of its battery life you probably don’t need a new battery. What you need is a malware scanner. Malware programs run in the background consuming memory, wireless connections, and subsequently the battery. Scan with a malware program from a trusted source. Also, check for firmware updates for the device.
Slow data speeds
Here is another indication of malware. When your connectivity is compromised you will experience slower than usual downloads and web page loads. This is caused by malware consuming your bandwidth to propagate. Obtain a malware scanner from a trusted source to check for malware.
Unintended WiFi connection
Malicious hotspots pose a serious threat to your data security along with the health and performance of your device. Many devices are configured to access any wireless connection based primarily on signal strength by default. Generally, hotspots offered as a customer service provide some sort of user validation for the connection. However malicious Wireless LANs (WLAN) will make unintended access to their rogue access points transparent. You will find yourself on a network constructed by a hacker consisting of you, other victims, and the evildoers. You will notice sub-par performance and blame it on the connection, while the fact is that your device is being plundered and malware is being loaded in the background. The trick to avoiding this is to configure your device Wi-Fi to ask before connecting giving you a chance to look at the SSID or to disable all automatic connections. The name of the setting will differ but the intent is clear. You should also turn your Wi-Fi off when not in use.
Click here for the A+ Practice Test Bundle for A+ Exams 220-1001 & 220-1002
Unintended Bluetooth pairing
Even though Bluetooth is described as a low-power short-range connection type you are vulnerable to those in your range. This could easily be a fellow commuter, diner, or coffee drinker. If your Bluetooth is always on a hacker can easily connect to your device while it’s in your pocket. Be sure to disable Bluetooth when it is not being used. In addition to the security, your battery life will be improved.

Bluetooth
Leaked personal files/data
The term data leakage refers to the unauthorized transmission of data from a trusted entity (internal) to an untrusted entity. Data leakage can be in the form of electronic channels like email, HTTP, or P2P, and others. Physical media like USB drives and other storage media can transport leaked data out of the trusted space and also provide an open door for inbound malware piggybacking on the devices. A great example of this technique is a program called slurp. This program can reside on a portable media player or other electronic devices like a smartphone or tablet, and when connected to a PC it can copy all documents spreadsheets, and presentations. Leaks can be malicious or inadvertent in nature. When overall leakage was examined it turned out that only about 1% were malicious internal leaks. The others were inadvertent leaks and attributed to poor business data handling or simple employee oversight. Internal leaks can be attributed to malware, email, webmail, and file sharing. External leaks would include intruders or hackers who tailor exploits to suit their needs using malware.
Data transmission over the limit
Ok this one’s easy. Your phone sits idle for most of the day. Then you get a warning from your service provider that you are over your usage allowance for your plan. You have never been close to maxing out your plan. Now, you have to go the rest of the month at 3G instead of 4G. The ever-present threat…Malware alive and well on your device! When you see unusual behavior like this on your device it could be due to malicious programming that doesn’t close when you shut it down. It either resurfaces or even worse runs in the background completing its tasks. This can have a serious impact on your data usage, throughput, and battery life.
Unauthorized account access
If your device has been compromised you should always consider which online accounts you have accessed with the device. Once a hacker is on the inside they can extract your credentials. Check all of your accounts and change the passwords as soon as you can using a clean uncompromised device. Do not make your changes from the compromised device, as aside from the false sense of security, you will be updating the hacker information and possibly identifying new targets. This information will provide them the usernames and passwords for specific accounts and in many cases, this information will provide the foundation for hackers to target their attempts for other accounts.
Unauthorized root access
In terms of permission and capabilities rooting an Android device and jailbreaking an iOS device represent the highest level of command and control available. For Android, the only real limit is the user’s skill set. Intentionally rooting or jailbreaking a device is useful but it is a good policy to unroot the device after you have accomplished your goal. Malware will root your device to enhance its capabilities. These capabilities include allowing span from editing system files to capture PII, replacing the operating system with rogue version, installing pre-jailbroken firmware or if damage is the hacker’s goal, the device can be turned into a brick. You can check this on Android with Root checking apps from the Play Store or looking for installed root apps like KingRoot, Vroot, or Framaroot to name a few. Jailbroken iOS devices may display new unfamiliar app icons on the home screen like RedSnow, Cydia, and JailbreakMe. In the majority of cases, the device can be unrooted with a factory reset/clean install.
Unauthorized location tracking
The GPS on your mobile device is useful for determining your current location within a few feet. This information can be combined with a mapping app to get directions or even to use search terms to find the goods and services you are looking for based on their proximity. So with the understanding of this behavior, it would be within reason that upon installation an advertising-based app would request access to the browser for advertising or business locations and certainly, the map app would be allowed to get the geolocation information. On installation conforming, apps will request the required features or data sets for your approval. If you deny this access the installation will usually terminate. Here is an example of the type of information that can be compromised and analyzed.
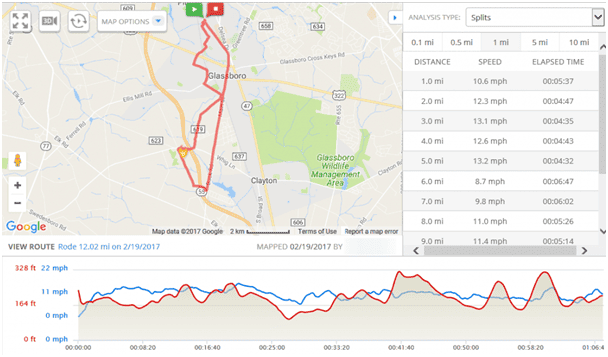
GPS Output
Unauthorized Camera/microphone activation
When you consider the camera(s) and microphone on your device it’s not hard to think of the privacy and security issues involved when a device is compromised. You will detect this type of unauthorized access by examining resource consumption particularly your internet performance. The audio and video are being streamed to the evildoers and the process can be revealed by the unusual amount of send/receive activity. This compromise also impacts performance and battery life. A hacker with access to the camera and microphone can collect and correlate this information and use apps like a PIN skimmer to determine exactly where you are looking when the audio reports a tap. Combine that information with the x/y tap location and there is a practically guaranteed result.
Click here for the A+ Practice Test Bundle for A+ Exams 220-1001 & 220-1002
High resource utilization
The utilization of your mobile device’s resources is the primary point to examine when you suspect a compromise. As we have been covering throughout this objective the majority of compromises can be tied to the way malware consumes system resources. The battery, internal storage, and data transmission rates will all reveal unauthorized activity. That is it for objective 3.5 which is the final objective in domain 3.0 Software Troubleshooting. See you in domain 4.0!

By continuing to browse this site, you accept the use of cookies and similar technologies that will allow the use of your data by CertBlaster in order to produce audience statistics- see our privacy policy.